What is Gateway in Computer Network – Types, Examples, Functions
The Crazy Programmer
SEPTEMBER 25, 2021
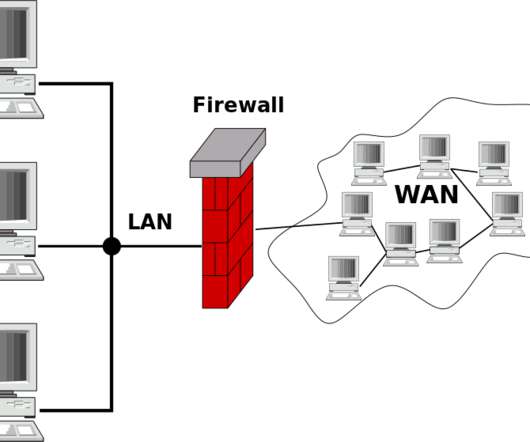
These devices can be the firewall, router, server, and other devices used for the networking and allow the flow of the data from one device to another device through their network. It allows broadcasting the available data in the form of video or audio among the devices through transmission. VoIP Trunk Gateway. Types of Gateway.
















Let's personalize your content