OpsMX Adds Deployment Firewall to Ensure Compliance
DevOps.com
OCTOBER 23, 2023
OpsMx announced it has added a deployment firewall to its Deploy Shield portfolio for securing CI/CD platforms.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

DevOps.com
OCTOBER 23, 2023
OpsMx announced it has added a deployment firewall to its Deploy Shield portfolio for securing CI/CD platforms.

CIO
JANUARY 4, 2024
However, managing PCI security compliance across various lines of business within these institutions can be a complex and resource-intensive task. The CCA allows overarching enterprise functions and IT shared services to be assessed separately from the business unit’s products/applications that require PCI security compliance.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

OTS Solutions
JUNE 21, 2023
However, as more organizations rely on these applications, the need for enterprise application security and compliance measures is becoming increasingly important. Breaches in security or compliance can result in legal liabilities, reputation damage, and financial losses.
Palo Alto Networks
SEPTEMBER 19, 2023
If you want to protect applications and workloads throughout today’s complex and interrelated environments, you need software firewalls. You can better understand the extensive need and numerous use cases for virtual firewalls, container firewalls and managed cloud firewalls with our essential guide, “ Software Firewalls for Dummies.”

OTS Solutions
JUNE 21, 2023
However, as more organizations rely on these applications, the need for enterprise application security and compliance measures is becoming increasingly important. Breaches in security or compliance can result in legal liabilities, reputation damage, and financial losses.
Firemon
OCTOBER 30, 2020
Just three years ago, technology headlines were rife with articles stating that the firewall was obsolete. And maybe that prophecy would have come true if we were stuck with the same old firewalls that could only perform simple packet filtering. Learn how FireMon Firewall Security solves your most complex problems.

Firemon
FEBRUARY 15, 2023
According to Gartner, 99% of firewall and cloud security failures can be attributed to errors in configuration. According to Gartner, 99% of firewall and cloud security failures can be attributed to errors in configuration. Policy Analyzer is a solution that delivers immediate value to firewall and security administrators.

TechCrunch
FEBRUARY 23, 2022
Secureframe currently covers some of the most well-used and well-known security and privacy compliance standards — HIPAA for health data, SOC 2 and ISO 27001 for information security, and PCI DSS for financial information. That is the main thing that is driving security standards compliance.”

Firemon
JULY 21, 2020
It’s an enormous and unending daily challenge to make sure that changes to firewall policies are not just executed quickly and efficiently, but changes don’t decrease the security of your network. Through the next several years, Gartner says that misconfiguration errors will be responsible for 99% of all firewall security breaches. .

Palo Alto Networks
OCTOBER 8, 2021
Take the industry’s leading virtual firewall for a no-obligation spin in your virtualized environments. It’s never been easier, thanks to our 30-day free trial to test the VM-Series virtual firewalls for VMware ESXi and Linux KVM environments. Boost compliance and risk management programs.

CIO
DECEMBER 18, 2023
Other fears cover compliance with emerging AI regulations and the risk of models becoming contaminated or biased through adversarial attacks. 4) Future of LLM firewall (proxy server) The LLMs could provide some sort of firewall capability similar to what we have now with the major cloud platforms.

Firemon
SEPTEMBER 28, 2020
This is part 2 of a 4-part series addressing compliance myths and what you need to know about uniting compliance and security in a hybrid environment. Many organizations have adopted a passive compliance playbook. Regulations continued to change, but firewall policies may or may not have been updated. Read part #1 here.

Firemon
FEBRUARY 14, 2024
How is FireMon Better Book a Demo Healthcare companies have a responsibility to protect sensitive patient data and ensure compliance with regulations like HIPAA. FireMon’s solutions provide enhanced network security, compliance management, and real-time visibility and control. Why Act Now? Why Choose FireMon? Why Act Now?

Datavail
APRIL 22, 2020
Perhaps the biggest reason to modernize your legacy system is that its elements are no longer able to keep your agency safe from criminals or up-to-date with compliance requirements. The second corporate safety concern is compliance – keeping your agency aligned with contractual and industrial rules and standards.

CircleCI
JULY 18, 2022
Compliance requirements can add significant overhead to an organization. Fortunately, it is possible to automate compliance-related activities using continuous integration and third-party tools. Examples of software compliance requirements. Software compliance best practices. Regular compliance audits.

Firemon
AUGUST 20, 2020
This is part 1 of a 4-part series addressing compliance myths and what you need to know about uniting compliance and security in a hybrid environment. People are confused about what compliance really is. Yet some businesses still think that if they can tick every box in a compliance checklist, they are secure.

CIO
FEBRUARY 7, 2023
Among the responses (edited slightly for clarity; this was Twitter, after all): – Lack of visibility/control over [network] activity – Complex compliance requirements compounded by lack of internal compliance expertise – Insider threats and malicious activity – and the list goes on and on @willkelly Easy to come up w/50 #cloud #infosec challenges.

Firemon
APRIL 11, 2023
These may involve: Achieving continuous compliance Risk reduction strategies Improving operational efficiencies and reducing costs Step 2: Develop Success Criteria Work with your FireMon Sales Engineer (SE) to create a list of success criteria that will help you assess FireMon’s technical capabilities.

CIO
DECEMBER 21, 2023
The diversification of payment methods and gradual increase in the volume of online transactions have cast a spotlight on the need for payment security compliance within the airline industry. released in March 2022, with mandatory compliance starting on March 31, 2024, represents an updated and refined version of the Standard.

Firemon
JANUARY 20, 2022
The post The Sweeter Side of PCI Compliance appeared first on FireMon.

CIO
JULY 11, 2022
Additionally, all security policies can be managed centrally, enabling IT administrators to implement security updates to all devices and users on the entire network quickly and easily, to help enable compliance. Comcast Business offers a unique set of secure network solutions to help power financial services organizations.

Linux Academy
JUNE 26, 2019
Failure to meet regulatory compliance spells serious trouble for your business. Compliance scanning. Here are a few steps you can take to meet regulatory compliance in your organization: System Auditing. To meet regulatory compliance, your organization needs an auditing process. Compliance Scanning. Access control.

Firemon
APRIL 12, 2023
In addition to our industry-leading security policy management, cloud security operations, and asset management solutions, come learn about some new, exciting announcements including… FireMon Cloud Defense – Real-time cloud compliance, inventory, misconfiguration, and threat detection. Now with proactive IAM defense.

TechCrunch
SEPTEMBER 23, 2021
This partially stems from misinformation surrounding technologies such as web application firewalls, and the current native browser defenses are severely lacking when it comes to effectively preventing client-side attacks.”. Jscrambler claims it addresses this shortfall. health privacy rules HIPAA.

TechCrunch
FEBRUARY 11, 2022
Microsoft spent $500 million in July to acquire RiskIQ, a company that provides visibility into what assets, devices and services can be accessed outside of a company’s firewall, describing the takeover as a “powerful” addition to its portfolio. Assets, assets everywhere. ”

Firemon
OCTOBER 19, 2020
To err is human, and with many enterprises managing 100 firewalls or more, there are plenty of chances for humans to err. Almost two out of every three businesses are still using manual firewall change management processes, despite ever-increasing volumes of change requests. The costs of managing firewalls are often hidden.

Firemon
JANUARY 3, 2019
The same goes for many of you who have to keep up with audits to maintain compliance with internal and regulatory mandates like the Payment Card Industry Data Security Standard (PCI-DSS) or the Health Information Trust Alliance (HITRUST). Click here to read how one of our customers got their compliance in shape with FireMon.

CIO
JANUARY 20, 2023
Better IoT Security Helps Ease Regulatory Compliance Challenges Understandably, there are a lot of compliance requirements in healthcare. Any attack that involves a patient system or medical IoT device is most likely a compliance breach, resulting in the loss of sensitive data or access to sensitive data from unauthorized entities.

Firemon
OCTOBER 13, 2020
This is part 3 of a 4-part series addressing compliance myths and what you need to know about uniting compliance and security in a hybrid environment. They can’t wave the white flag because compliance and access control are difficult and time-consuming for them. Learn the Truth about the 4 Myths of Security Policy Compliance.

CIO
APRIL 27, 2023
There’s an ever-growing need for technical pros who can handle the rapid pace of technology, ensuring businesses keep up with industry standards, compliance regulations, and emerging or disruptive technologies. Companies can’t ignore digital transformation as technology continues to dominate nearly every aspect of business and daily-life.

TechCrunch
OCTOBER 27, 2022
Access can be audited in real time, ostensibly making it easier for managers to produce compliance reports and analyze historical authorizations. The modern workforce is no longer operating from inside a corporate firewall using only on-premise applications,” Kriz added.
AWS Machine Learning - AI
JANUARY 26, 2024
Many customers are looking for guidance on how to manage security, privacy, and compliance as they develop generative AI applications. In addition to awareness, your teams should take action to account for generative AI in governance, assurance, and compliance validation practices.

Palo Alto Networks
MAY 7, 2024
Also, AI-SPM provides visibility into the entire AI ecosystem, including models, applications and resources, to reduce the risk of data exposure and compliance breaches. Integrate with AI firewalls to give your security teams the ability to secure your entire AI application ecosystem at runtime.

Firemon
MARCH 31, 2023
Ensure Compliance : Many industries have strict compliance requirements that organizations must meet to avoid penalties and fines. Asset visibility enables you to monitor and manage assets across your network, helping ensure compliance with regulations like HIPAA and PCI-DSS.
CIO
MARCH 13, 2023
Achieving these objectives takes perceptive analysis, meticulous planning, and skillful execution. “There are many factors to consider, including application complexity, legacy application requirements, data location, and compliance,” says Dilip Mishra, SAP delivery leader for the Cloud Migration and Modernization practice at Kyndryl.

Palo Alto Networks
OCTOBER 18, 2019
You might be surprised to learn that SSL decryption can be a valuable tool for protecting data in compliance with the European Union’s General Data Protection Regulation (GDPR), when applied according to best practices. A Plan for SSL Decryption and GDPR Compliance. To implement SSL decryption, you need buy-in within your organization.
CIO
NOVEMBER 2, 2023
The cloud: While many organizations have embraced the cloud, especially with the rise of work from anywhere (WFA), some companies must keep all their data and systems on-premises because they deal with highly regulated data or must meet strict compliance standards.

CIO
FEBRUARY 24, 2023
Are there any platforms that can handle our need to shift left, protect our runtime environment, and feed into our security operations, governance, and compliance; infrastructure architects’ workflows to provide visibility, protection, and auditing layers for our entire application landscape? We can help.
Firemon
SEPTEMBER 16, 2022
The most common threat to business security is accidental firewall and cloud security group misconfigurations. The average enterprise network team is asked to make more than 100 firewall changes per week, and these changes can then take weeks to manually implement. Problem 1: Time-consuming Manual Changes.
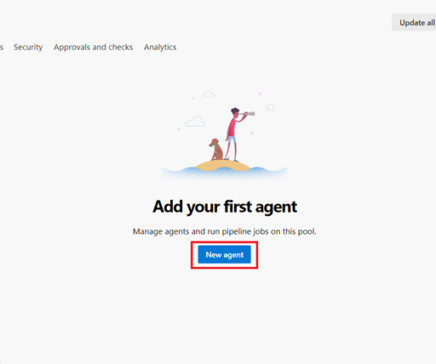
Perficient
NOVEMBER 21, 2023
Security and Compliance: Self-hosted agents offer greater control over security measures and compliance requirements. Firewall Configurations: Users can manage firewall configurations to control network access for self-hosted agents, enhancing security and compliance.

Firemon
JUNE 26, 2020
Misconfigurations, in turn, raise the likelihood of compliance failures. Cloud complexity emerges because public cloud configuration isn’t automatically linked to firewall policy configuration. Yet, just like firewalls, public cloud instances accumulate unused and redundant rules. Missing information leads to misconfigurations

Palo Alto Networks
JUNE 17, 2020
Container adoption is on a serious rise, which is why we’re releasing CN-Series , the containerized version of our ML-Powered Next-Generation Firewall (NGFW), designed specifically for Kubernetes environments. CN-Series container firewalls deployed on each node in the environment for maximum visibility and control.

Firemon
APRIL 2, 2020
Before working for FireMon, I was a cybersecurity professional at a Fortune 500 where I inherited a lot of firewalls with a lot of rules. While in the trenches, I was always looking to address the “3 Cs”— change, compliance, and clean up. As a cybersecurity professional, it’s easy to get the nickname “Dr.

Lacework
JULY 18, 2022
For many years, the ISO 27001 certification has been an industry benchmark to show compliance with standard security practices. If you’ve never worked in compliance before, there can be the impression that achieving compliance is a simple checklist when in fact, the opposite is true. It is of course our job to protect it.
Expert insights. Personalized for you.
Are you sure you want to cancel your subscriptions?


Let's personalize your content