Mitigating cyber risks: the essential role of collaboration for Middle East organizations
CIO
OCTOBER 21, 2024
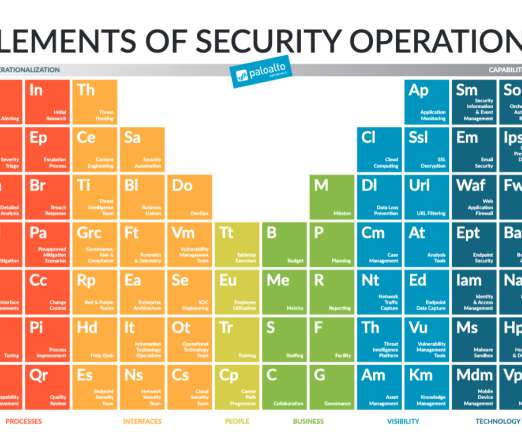
At Gitex Global 2024, a panel of top cybersecurity leaders delivered a clear message: cybersecurity is no longer just the responsibility of the cybersecurity team or the Chief Information Security Officer (CISO). These areas, often neglected or poorly managed, can expose businesses to serious vulnerabilities.











































Let's personalize your content