INE Security Alert: The Steep Cost of Neglecting Cybersecurity Training
CIO
AUGUST 20, 2024
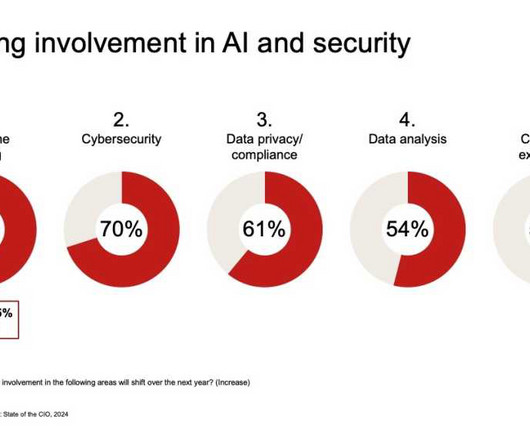
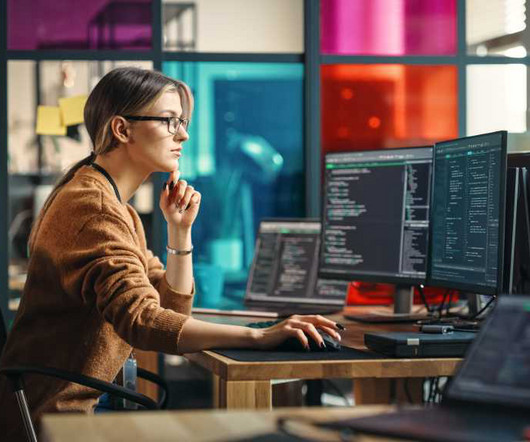
In modern business, cybersecurity is not merely a technical concern but a crucial financial safeguard. With cyber threats growing in sophistication and frequency, the financial implications of neglecting cybersecurity training are severe and multifaceted. The average cost of a data breach ballooned to $4.88















































Let's personalize your content