6 steps the manufacturer of Arm & Hammer and OxiClean took to harden OT cybersecurity
CIO
APRIL 30, 2024
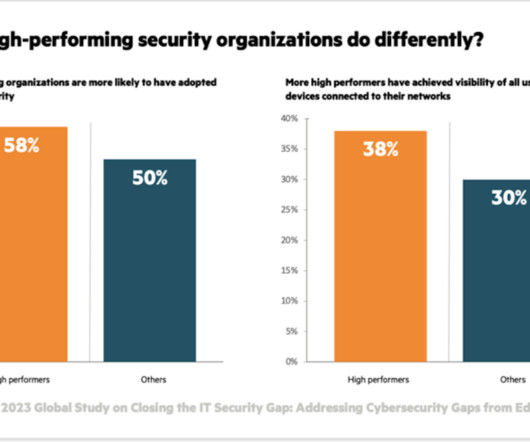
The threat of cyberattack has never been higher, and nearly nine in 10 (88%) of security leaders believe their organization is not meeting the challenge of addressing security risks, according to the Foundry Security Priorities Study 2023. Specifically, we needed to better protect OT operations,” Ortiz explained. “At

















































Let's personalize your content