Predator Spyware Resurfaces With Fresh Infrastructure
Ooda Loop
SEPTEMBER 9, 2024
The Predator spyware has resurfaced with fresh infrastructure after a drop in activity caused by US sanctions against Intellexa Consortium, Recorded Future reports.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Ooda Loop
SEPTEMBER 9, 2024
The Predator spyware has resurfaced with fresh infrastructure after a drop in activity caused by US sanctions against Intellexa Consortium, Recorded Future reports.

TechCrunch
SEPTEMBER 27, 2021
Mobile spyware is one of the most invasive and targeted kinds of unregulated surveillance, since it can be used to track where you go, who you see and what you talk about. And because of its stealthy nature, mobile spyware can be nearly impossible to detect. “We already know applications that are spyware.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Launching LLM-Based Products: From Concept to Cash in 90 Days
How To Speak The Language Of Financial Success In Product Management
The AI Superhero Approach to Product Management
How to Select the Perfect Payments Partner: 7 Keys for Sustainable Growth
Building Your BI Strategy: How to Choose a Solution That Scales and Delivers

Ooda Loop
JULY 31, 2024
Five applications were discovered to have been carrying a version of the Mandrake Android Spyware on Google Play for two years. Mandrake is a spyware platform which allows attackers to completely control infected devices. During the applications’ time on Google Play, they had over 32,000 downloads. The attackers can record […]
Launching LLM-Based Products: From Concept to Cash in 90 Days
How To Speak The Language Of Financial Success In Product Management
The AI Superhero Approach to Product Management
How to Select the Perfect Payments Partner: 7 Keys for Sustainable Growth
Building Your BI Strategy: How to Choose a Solution That Scales and Delivers

Ooda Loop
MAY 28, 2024
In a weekly news roundup, Chinese radar ships might be spying on undersea communications, spyware found at hotel check-ins, and Iran continues disruptive attacks. This week, consumer-grade spyware was discovered in Wyndham hotels across the United States.

Ooda Loop
APRIL 11, 2024
‘EXotic Visit’, an Android malware campaign has been targeting users located in South Asia from the Google Play Store. The cybersecurity firm Slovak has been tracking the campaign since November 2021 using the moniker Virtual Invaders. No known threat actor group is linked to the campaign. EXotic Visit is also […]
Strategy Driven
APRIL 11, 2023
As secure as Apple devices are, unfortunately, there’s no guaranteed way to ensure that they won’t fall foul of malware sneaking its way onto the devices from time to time. Adware Cleaner According to Apple , one of the easiest ways for spyware, trojans and malware in general to make their way onto devices is via Ads.

Ivanti
JUNE 3, 2024
Spyware : Spyware kits, services and source code are commonly traded and shared on the dark web — and even on mainstream repositories like GitHub or online communities like Reddit. Malware : The vast majority of Android malware is delivered from third-party app stores.

The Parallax
FEBRUARY 18, 2020
SAN FRANCISCO—The greatest trick stalkerware, one of the most dangerous forms of malware , ever played was convincing the world that it didn’t exist. Until recently, cybersecurity experts could overlook stalkerware because of the personal nature of how it spreads, its muddled legal status—and how it is detected.
CIO
NOVEMBER 8, 2023
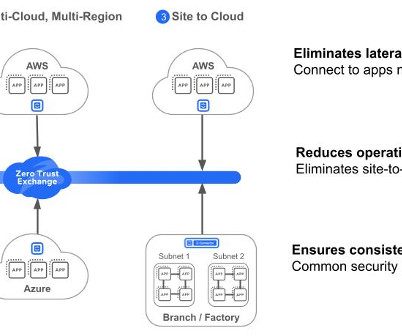
Why securing cloud workloads is an urgent matter In recent years, major cloud service providers encountered 6,000 malware samples actively communicating with them, underlining the magnitude of cloud security challenges. 3 We have seen an increase of 15% in cloud security breaches as compared to last year. 8 Complexity.

Dzone - DevOps
FEBRUARY 23, 2023
Summary It is of utmost importance for enterprises to protect their IT workloads, running either on AWS or other clouds, against a broad range of malware (including computer viruses, worms, spyware, botnet software, ransomware, etc.

The Parallax
MAY 7, 2018
Malware and antivirus software usually go together like tacos and pickles. Researchers announced on May 1 that when they inspected the ingredients of the North Korean antivirus software for Windows computers, they found a mix of spyware and old code stolen from an antivirus vendor.
Symantec
NOVEMBER 29, 2023
A look at some deceptive tactics used by malware authors in an effort to evade analysis.

The Parallax
JANUARY 22, 2018
Its success was predicated not on “zero-day” vulnerabilities or new forms of malicious software, but rather on older, known malware delivered via an all-too-familiar method: phishing. The malware included hacked versions of end-to-end encrypted communication apps Signal and WhatsApp.

TechBeacon
APRIL 4, 2019
At least, that’s what some conclude, after hearing about Exodus , a family of targeted malware discovered in the official Google Play app store. The sky is falling.

Storm Consulting
NOVEMBER 21, 2023
It helps torrenting, has a effective destroy switch and split tunneling, as well as a menace manager that blocks advertisements, malware and trackers. While absolutely free options like Betternet are tempting, they have concerns such as not enough a reliable wipe out switch, DNS leaks and an extremely poor logging plan.

Storm Consulting
NOVEMBER 7, 2023
When it comes to virus safety reviews, the most important factor is how well a program helps to protect against spyware and adware. This includes the two viruses and spyware, that may steal personal information and gradual down your computer.

Storm Consulting
NOVEMBER 4, 2023
For laptop or computer gamers, the ideal antivirus applications are one that protects devices from malware dangers while lessening the impact on gambling performance. It also illustrates excellent adware and spyware detection rates and uses heuristic diagnosis to get malware certainly not yet exist in its database.

Tenable
MARCH 1, 2024
And the most prevalent malware in Q4. In these attacks, users are tricked into installing what they think is a legitimate browser update that in reality is malware that infects their computers. It’s been a meteoric rise for SocGholish, which first cracked the CIS list in the third quarter, with a 31% share of malware incidents.

Storm Consulting
NOVEMBER 25, 2023
Developed by cybersecurity service provider Lavasoft (formerly referred to as Ad-Aware), adaware assessment is designed to cures spyware risks like applications that observe your surfing around habits or hijack your home page. In the last test run by AV-Test, it were able to eliminate every one of the tested malware but just blocked 94.

Ivanti
JANUARY 19, 2022
Ransomware, on the other hand, was responsible for most data breaches caused by malware. against known and zero-day vulnerabilities, zero-click exploit kits developed by the NSO Group, fileless malware and the adoption of the “as-a-service” business model. Ransomware is malware whose sole purpose is to extort money from the end user.

Storm Consulting
OCTOBER 4, 2023
Produced by cybersecurity corporation Lavasoft, adaware is definitely an antivirus security software program designed to fight off the types of malware that bog down your computer – courses that keep tabs on searching habits and lessons that hijack browser start pages and slam you with troublesome advertisements. some percent of threats.

Tenable
FEBRUARY 22, 2021
A vulnerability could also be a host on the network that lacks modern protections like next-generation firewalls or anti-malware features. Keep in mind that “vulnerability” isn't a synonym for words like "malware," "virus," "trojan" or any of the other words that describe common cyberthreats. Try Nessus Free for 7 Days.

Lacework
JANUARY 25, 2023
Whether you’re facing a sophisticated phishing attack or a form of never-before-seen malware (also known as an “unknown threat” or “unknown unknown”), threat detection and response solutions can help you find, address, and remediate the security issues in your environment. If not detected, malware can cause downtime and security breaches.

Ivanti
SEPTEMBER 9, 2021
The quickest method to check for the presence of malware on your iPhone, iPad or macOS devices is to look for the presence of an unknown configuration profile within the Settings > General > VPN & Device Management settings. Victims would then be coerced to pay money to remove the malware from their devices or laptops.

Palo Alto Networks
MAY 2, 2023
Then there’s Advanced Threat Protection , which stops unknown exploits, malware, spyware and command and control (C2) while utilizing inline deep learning to halt zero-day attacks in real time. Even more capabilities come with Cloud NGFW for Azure. Advanced URL Filtering has been designed to stop malicious URLs.

KitelyTech
APRIL 11, 2023
For example, you don’t want users to try to use your app for illegal purposes, like generating code using GPT-J to create viruses or malware. That way, users asking for “malware” or “spyware”, for example, will have their requests blocked and receive a templated message saying that what they asked for is not allowed.

KitelyTech
JANUARY 11, 2019
Malware refers to any software that’s installed on a computer or any machine to carry out unwanted tasks benefiting a third party. Examples of malware include spyware, Trojans, adware, ransomware and bots. In addition, SMEs should have secure backups for crucial data.

Tenable
MAY 28, 2020
Malware: This catch-all term encompasses a number of different cybersecurity threats, including everything from viruses and worms to banking trojans, adware, spyware and ransomware. In terms of specific threats, a bank, for example, should probably be most concerned about the various classes of ATM malware (two dozen or more 9 ).

iTexico
FEBRUARY 4, 2020
AI applications are helping businesses stay ahead of these threats by detecting potentially malicious activities by utilizing complex algorithms to pattern recognize and detect viruses and malware. AI can also analyze data across multiple channels to identify spyware and malware before they hurt your system. Malware threats.

Kaseya
OCTOBER 3, 2023
Due to its ability to detect new-age threats, like zero-day and fileless malware, that are stealthy enough to bypass conventional AV and AM solutions, EDR is a must-have in today’s increasingly dangerous cybersecurity environment. The infection can be a virus, trojan horse, worm, spyware, adware, rootkit or the infamous ransomware.

CTOvision
APRIL 28, 2014
They do what it takes to get in, including devising very sophisticated phishing schemes, creating spyware, placing code in RAM, leaving hacker tools, installing rootkits and continually adjusting/re-placing spyware. The exact code will of course vary, but they will implant it in your enterprise. Then it will communicate out.

InfoBest
DECEMBER 14, 2021
Not to mention that malware kits are available on the dark web, so even criminals without IT knowledge can orchestrate attacks. Malware is a term used for malicious software in general. Some of its variations are spyware, ransomware, viruses, worms, and so on. They sometimes also install malware on the device used. .

Tenable
OCTOBER 28, 2022
Restrict Server Message Block Protocol within the network because it’s used to propagate malware. 6 - And here’s the CIS top 10 malware list for September. TeamSpy, spyware that uses remote access tool TeamViewer and malware to steal information. NanoCore, a RAT that spreads via malspam as a malicious Excel spreadsheet.

Altexsoft
JUNE 2, 2020
You can classify a binary file into categories like legitimate software, adware, ransomware, and spyware. Zimperium and MobileIron announced a collaboration to help organizations adopt mobile anti-malware solutions incorporating artificial intelligence. Hackers also use AI —to improve and enhance their malware. by 80% by 2050.
O'Reilly Media - Ideas
DECEMBER 6, 2022
The popularity of cryptojacking (mining cryptocurrency with malware planted in someone else’s applications) continues to rise, as the collapse in cryptocurrency prices makes legitimate mining unprofitable. A threat group named Worok is using steganography to hide malware within PNG images.

KitelyTech
SEPTEMBER 27, 2021
The biggest problem with MSM is that it can be exploited to download spyware and malware onto your phone. Users reported that MSM uses a lot of mobile data, which can increase your bill. It also takes up a lot of storage space, which users do not like. Attempts have been made to exploit MSM for these purposes.
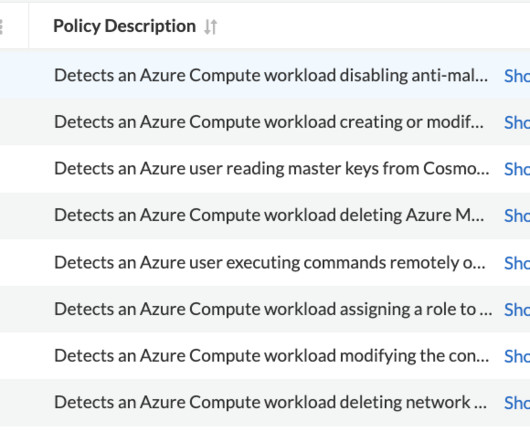
Prisma Clud
APRIL 20, 2023
Antimalware for Azure is a protection capability that helps identify and remove viruses, spyware, and other malicious software. Attackers often attempt to disable these extensions in order to deploy malware. Azure User Reading Database Master Keys This policy detects an Azure user reading master keys from Cosmos DB.
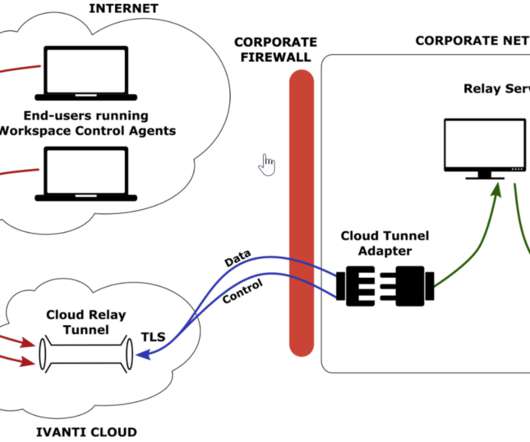
Ivanti
MARCH 9, 2022
This prevents potentially dangerous executables containing viruses, spyware, and malware from contaminating the corporate network. The end-users are prevented from running executables that they might receive through e-mail or the Internet. Integration.
O'Reilly Media - Ideas
AUGUST 2, 2021
There’s a new technique for protecting natural language systems from attack by misinformation and malware bots: using honeypots to capture attackers’ key phrases proactively, and incorporate defenses into the training process. But Google Glass showed the way, and that path is being followed by Apple and Facebook in their product development.

CTOvision
FEBRUARY 24, 2017
While companies go to the cloud, they also need professionals with network security management skills to survey the on-goings within the network and pinpoint suspicious behavior, as well as develop on-point and immediate counter measures should malware or spyware successfully find its way into the system. Detecting Cyber Intrusions.

Altexsoft
FEBRUARY 6, 2021
Viruses and other malware can create various adverse consequences that usually require companies to halt their systems until the malware is removed. Moreover, spyware can result in data losses that can also mean disruptions in business operations.

Palo Alto Networks
JANUARY 23, 2023
It is specifically designed to identify infected devices and block known exploits, malware, malicious URLs and spyware in 5G environments. With state CIOs focused on strengthening statewide connectivity, expanding rural broadband and deploying 5G, mobile users and devices are more at risk than ever.

Hu's Place - HitachiVantara
MAY 10, 2019
These new technologies open up new risks such as phishing, identity theft, card skimming, viruses and Trojans, spyware and adware, social engineering, website cloning and cyber stalking and vishing (If you have a mobile phone, you’ve likely had to contend with the increasing number and sophistication of vishing scams).

TechCrunch
DECEMBER 1, 2023
Apple has released security updates for iPhones, iPads and Macs to patch against two vulnerabilities, which the company says are being actively exploited to hack people. The technology giant rolled out new software updates, iOS and iPadOS 17.1.2, and macOS 14.1.2,
Expert insights. Personalized for you.
Are you sure you want to cancel your subscriptions?


Let's personalize your content