IoT Adoption in Healthcare Brings Security Opportunities
CIO
JANUARY 20, 2023
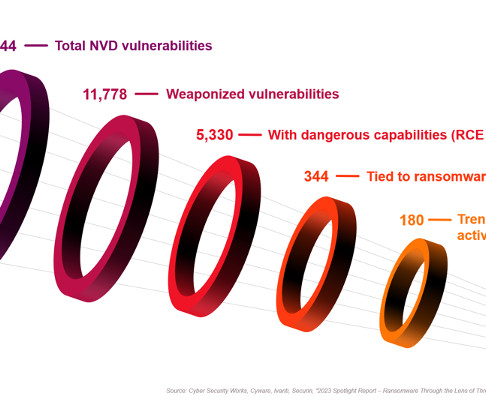
By Anand Oswal, Senior Vice President and GM at cyber security leader Palo Alto Networks Connected medical devices, also known as the Internet of Medical Things or IoMT, are revolutionizing healthcare, not only from an operational standpoint but related to patient care. But ransomware isn’t the only risk.

















































Let's personalize your content