Yes, you have to update your Apple devices again, because spyware is bad
TechCrunch
SEPTEMBER 22, 2023
Apple has released urgent security updates for iPhones, iPads, Macs, Apple Watch, and Safari users to block two active spyware campaigns.
This site uses cookies to improve your experience. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country, we will assume you are from the United States. Select your Cookie Settings or view our Privacy Policy and Terms of Use.
Cookies and similar technologies are used on this website for proper function of the website, for tracking performance analytics and for marketing purposes. We and some of our third-party providers may use cookie data for various purposes. Please review the cookie settings below and choose your preference.
Used for the proper function of the website
Used for monitoring website traffic and interactions
Cookies and similar technologies are used on this website for proper function of the website, for tracking performance analytics and for marketing purposes. We and some of our third-party providers may use cookie data for various purposes. Please review the cookie settings below and choose your preference.

TechCrunch
SEPTEMBER 22, 2023
Apple has released urgent security updates for iPhones, iPads, Macs, Apple Watch, and Safari users to block two active spyware campaigns.

TechCrunch
SEPTEMBER 27, 2021
Mobile spyware is one of the most invasive and targeted kinds of unregulated surveillance, since it can be used to track where you go, who you see and what you talk about. And because of its stealthy nature, mobile spyware can be nearly impossible to detect. “We already know applications that are spyware.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

TechCrunch
OCTOBER 4, 2023
Microsoft has released patches to fix zero-day vulnerabilities in two popular open source libraries that affect several Microsoft products, including Skype, Teams and its Edge browser. But Microsoft won’t say if those zero-days were exploited to target its products, or if the company knows either way.
TechCrunch
APRIL 11, 2023
” Small towns and local governments are largely unable to fend off ransomware attacks on their own. Can governments keep cyberspace safe and protect our information without compromising its values or violating human rights? If you haven’t noticed, the internet is frequently on fire. Just how on fire are we ?

TechCrunch
JULY 15, 2022
Journalists and activists are increasingly targeted by the wealthy and resourceful who seek to keep the truth hidden, from nation-state aligned hackers hacking into journalist’s inboxes to governments deploying mobile spyware to snoop on their most vocal critics. Turn on two-factor authentication!

The Parallax
MAY 7, 2018
Researchers announced on May 1 that when they inspected the ingredients of the North Korean antivirus software for Windows computers, they found a mix of spyware and old code stolen from an antivirus vendor. How antivirus software could be used for government espionage. China evaluates vulnerabilities for attacks before disclosure.

TechCrunch
JANUARY 11, 2022
Today we have new venture funds, spyware news, Brex raising (again), and more. Cybersecurity matters to democracy : Spyware built by the infamous NSO Group was “used to spy on three critics of the Polish government,” according to Citizen Lab, TechCrunch reports. Hello and welcome to Daily Crunch for January 11, 2022!

Ooda Loop
SEPTEMBER 9, 2024
The Predator spyware has resurfaced with fresh infrastructure after a drop in activity caused by US sanctions against Intellexa Consortium, Recorded Future reports.

TechCrunch
MARCH 11, 2022
EU to investigate state use of spyware : The Pegasus mobile spyware is causing headaches in Europe for more than just the folks who found themselves targets of the software. We have your full news digest below, but stay hype about TechCrunch Sessions: Mobility , because it’s looking increasingly lit. The TechCrunch Top 3.

The Parallax
JANUARY 22, 2018
Dark Caracal’s custom-developed mobile spyware, which the report’s authors call Pallas, is the first documented global advanced persistent threat , or APT, on a mobile device. However, Citizen Lab identified in a 2015 report the GDGS as one of two Lebanese government organizations using FinFisher surveillance software.

TechBeacon
SEPTEMBER 16, 2022
Once the message is opened (or, possibly, even if it's not), the victimized endpoint is at the mercy of the spyware’s commands. The story is as old as phishing itself. A malicious message is sent, disguised as something innocuous.
Ooda Loop
FEBRUARY 6, 2024
Governments seeking to spy on dissidents and people of interest to them have driven a proliferation in commercial spyware vendors in recent years, with more cyber-weapons brokers entering the market. What was the domain of the Israel-based NSO Group is not crowded with small CSVs with varying levels of sophistication […]

CTOvision
JULY 6, 2015
Google-style recruiting — even in government FCW (Today) - Hire people who are better than you, and make sure they’re smart and curious, says Google exec Laszlo Bock.Google is famous for its culture of work as play. Dezzutti has been instrumental in Market Connections’ efforts to provide views and trends to government.

Ivanti
JUNE 3, 2024
Spyware : Spyware kits, services and source code are commonly traded and shared on the dark web — and even on mainstream repositories like GitHub or online communities like Reddit. And, the average user is six to 10 times more likely to fall for an SMS phishing attack than an email-based one.
O'Reilly Media - Ideas
AUGUST 2, 2021
Amnesty International has released an open source tool for checking whether a phone has been compromised by Pegasus, the spyware sold by the NSO group to many governments, and used (among other things) to track journalists. Matthew Green’s perspective on “ security nihilism ” discusses the NSO’s activity; it is a must-read. Operations.
CTOvision
DECEMBER 4, 2014
Regin, new computer spyware, discovered by Symantec. Symantec says the bug, named Regin, was probably created by a government and has been used for six years against a range … Read more on BBC News. We believe our enterprise and government customers will be looking to focus on connecting technology innovation on a global scale.

Tenable
MAY 28, 2020
Malware: This catch-all term encompasses a number of different cybersecurity threats, including everything from viruses and worms to banking trojans, adware, spyware and ransomware. National Law Review, "State And Local Governments Continue To Be Favorite Targets Of Cyberattacks," September 2019 8.

TechCrunch
DECEMBER 1, 2023
Apple has released security updates for iPhones, iPads and Macs to patch against two vulnerabilities, which the company says are being actively exploited to hack people. The technology giant rolled out new software updates, iOS and iPadOS 17.1.2, and macOS 14.1.2,
O'Reilly Media - Ideas
DECEMBER 6, 2022
AI governance –including the ability to explain and audit results–is a necessity if AI is going to thrive in an era of declining public trust and increasing regulation. These companies are involved in activities like planting spyware on web sites to collect users’ personal data.

Tenable
MAY 7, 2020
Ransomware attacks are particularly and increasingly prevalent, especially against health care facilities and state or local government agencies. Ransomware attacks on US local governments and healthcare providers are on the rise , CNN, October 8, 2019 4. 3 And the types of ransomware deployed are more complex than ever.
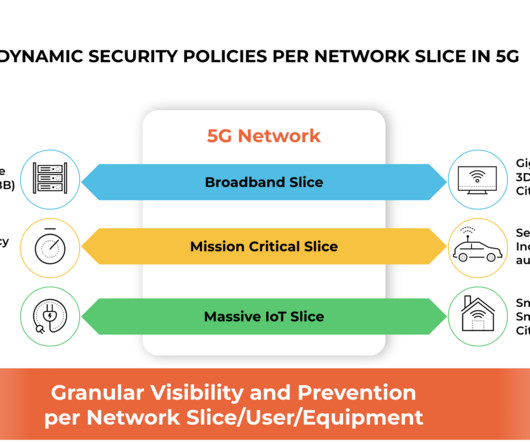
Palo Alto Networks
FEBRUARY 27, 2023
5G allows service providers the ability to offer different, dedicated, end-to-end network slices with different bandwidth and quality of service (QoS) to different enterprises, vertical industries and government agencies on the same 5G network simultaneously.

Palo Alto Networks
JANUARY 23, 2023
Priority #2: Digital Government/Digital Services Having a consistent cybersecurity posture is now more important than ever. Most state and local government agencies have a patchwork of nonintegrated, siloed security solutions of various maturity levels across their business networks, endpoints and clouds.

Hu's Place - HitachiVantara
MAY 10, 2019
These new technologies open up new risks such as phishing, identity theft, card skimming, viruses and Trojans, spyware and adware, social engineering, website cloning and cyber stalking and vishing (If you have a mobile phone, you’ve likely had to contend with the increasing number and sophistication of vishing scams).

Tenable
FEBRUARY 22, 2021
Spyware: Programs that monitor activity of infected computers (e.g., Tools like Nessus Professional can conduct compliance scans to determine adherence to cybersecurity protocols with government regulations, as well as industry standards like PCI DSS. Trojans: Malware disguised as programs or files a user needs.

Tenable
AUGUST 30, 2024
organizations with ransomware for financial gain, while separately stealing data on behalf of Iran’s government from U.S., That’s according to the Google Threat Analysis Group (TAG), which this week said that over the past nine months, multiple exploit campaigns were delivered via a watering hole attack on Mongolian government websites.

Tenable
MARCH 1, 2024
places stronger emphasis on governance, features broader scope The much awaited revamping of the National Institute of Standards and Technology’s (NIST) Cybersecurity Framework (CSF) is finally here. And the most prevalent malware in Q4. And much more! Dive into six things that are top of mind for the week ending March 1. came out in 2014.

Samanage
JANUARY 29, 2019
In fact, by the midpoint of 2018, the IT Governance Blog reported that there had already been more than 600 data breaches that year. Suffice it to say, hacking is on the rise and affecting more and more institutions, from government agencies to private and publicly held companies to universities.

Altexsoft
FEBRUARY 6, 2021
MITRE is the name of a US government-funded organization with a substantial cybersecurity practice spun out of MIT in 1958. Moreover, spyware can result in data losses that can also mean disruptions in business operations. The second word in MITRE ATT&CK® stands for Adversarial Tactics, Techniques, and Common Knowledge.
O'Reilly Media - Ideas
MARCH 15, 2022
One example of a mobile application security threat can be an individual downloading apps that look legitimate but are actually spyware and malware aimed at stealing personal and business information.

Tenable
OCTOBER 7, 2022
The document’s requirements include that by April 3, 2023 civilian executive-branch agencies of the federal government be able to: Perform automated discovery of IP-addressable networked assets that are on-prem, remote and in the cloud every seven days. government details hack of defense organization. Department of Homeland Security).

Tenable
OCTOBER 28, 2022
federal government, CISA encourages all organizations to read, pilot and react to them. 5 - Government warns healthcare orgs about new cybercrime group. government. TeamSpy, spyware that uses remote access tool TeamViewer and malware to steal information. For more information, read the CISA announcement.
Kaseya
DECEMBER 28, 2021
In the current economic climate, customers and clients prefer to do business with companies that have effective security measures in place and are compliant with government-issued cybersecurity guidelines. In the wake of a data breach, 60% of companies fail or go out of business. . How does endpoint protection work? .

O'Reilly Media - Ideas
OCTOBER 8, 2024
are concerned about spyware, 7.6% This exam focuses on issues like risk assessment, governance, and incident response—functions that certainly showed up in our question about job roles. Only 10.0% about illegitimate use of resources (for example, cryptocurrency mining), and 1.9% about becoming part of a botnet. Figure 1-2.

Mobilunity
DECEMBER 30, 2022
This gives hackers access to sensitive data on your computer and allows them to use spyware to monitor you in the background. Phishers send urgent messages via text, phone, or email posing as well-known businesses or government agencies. Your device will be infected if you click on the link. Making use of out-of-date software.

Kaseya
OCTOBER 3, 2023
The infection can be a virus, trojan horse, worm, spyware, adware, rootkit or the infamous ransomware. As nation-state cybercrime grows more common, every business is at risk from APT threat actors who are more than happy to exploit vulnerabilities to do the dirty work that enables them to strike at government and infrastructure targets.

Kaseya
SEPTEMBER 21, 2021
The infection can take the form of a virus, Trojan horse, worm, spyware, adware, rootkit or other malware like ransomware. A zero-day attack occurs when a hacker identifies any of these vulnerabilities, writes an exploit code and successfully deploys the code, also known as malware, to gain unauthorized access to a computer system or network.

TechCrunch
JULY 6, 2022
government that North Korean hackers are targeting some of the country’s healthcare organizations with their ransomware. Meanwhile, Zack reports that Apple’s new lockdown mode “will switch off certain features aimed at helping targeted individuals combat government-grade spyware.”. She also laid out a claim by the U.S.
TechCrunch
AUGUST 11, 2023
Oh, governments. The Chinese government is in uproar after Biden bans U.S. The Chinese government is in uproar after Biden bans U.S. Eye see you : A Kenyan government agency suspended Worldcoin’s activities, citing concerns with “authenticity and legality.” They do try ever so hard. this week.
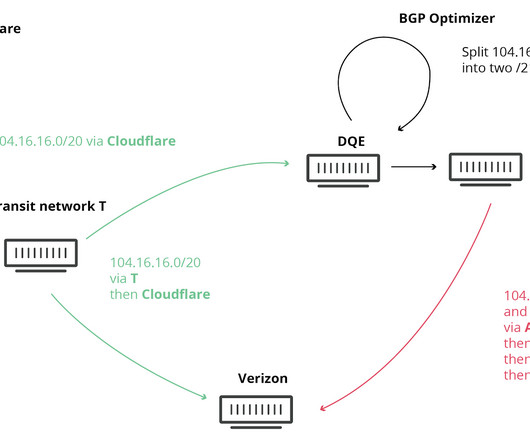
Kentik
JUNE 5, 2023
In that instance, the government of Pakistan ordered access to YouTube to be blocked in the country due to a video it deemed anti-Islamic. Origination errors can also include incidents that weren’t completely accidental, more commonly referred to as BGP hijacks.
CircleCI
JUNE 30, 2022
Because of how big and convoluted the software supply chain can get, risk-averse businesses and governments usually request a software bill of materials (SBOM) that describes a part or most of the supply chain. Attackers can compromise IAM controls through employees or systems to introduce spyware and ransomware.

The Daily WTF
JANUARY 20, 2025
TikTok, like every other social media company, is basically spyware, tracking your behavior to sell your eyeballs to advertisers. But as a quick recap: TikTok is owned by Bytedance, which is based in China, and subject to Chinese laws. All in all, it looks bleak. There's no easy fix for any of this.
Expert insights. Personalized for you.
Are you sure you want to cancel your subscriptions?


Let's personalize your content