Why are cybersecurity asset management startups so hot right now?
TechCrunch
FEBRUARY 11, 2022
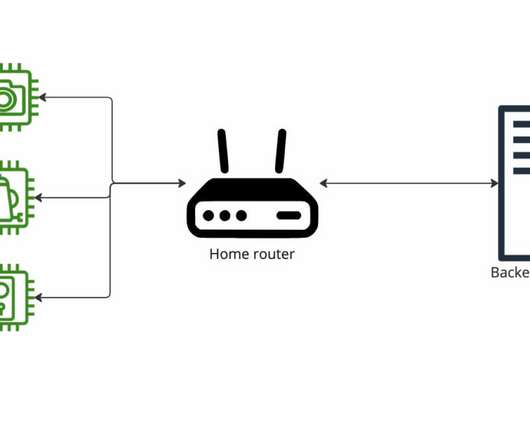
In the world of cybersecurity, you can’t secure something if you don’t know it’s there. Enter cybersecurity asset management, an admittedly unsexy fragment of the booming industry that investors have shown an ever-increasing appetite for over the past 18 months. Assets, assets everywhere. Shawn Cherian. ” . ”
















































Let's personalize your content