How to Develop IoT Applications: A Complete Guide for 2022
The Crazy Programmer
APRIL 24, 2022
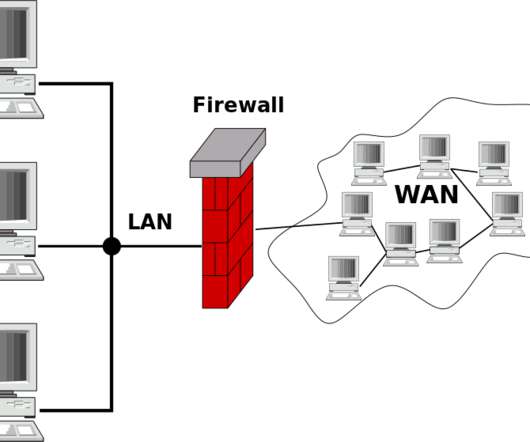
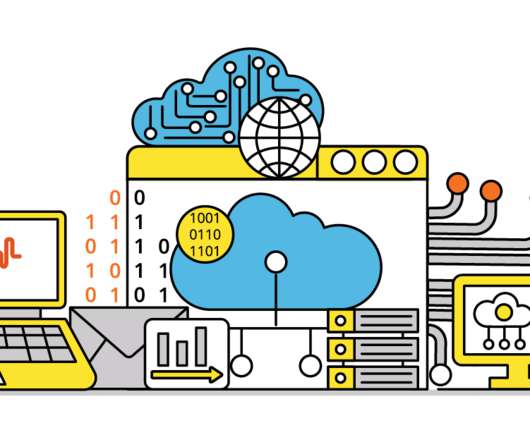
The software is crucial because it links to the hardware through the cloud and the network. Hardware: Hardware includes sensors, chips, and other measuring appliances. The creators of an IoT application must ensure that the software is compatible with the software’s hardware. 4 Stages of Building an IoT App.


















Let's personalize your content