Due diligence is ever more critical as the battle for cloud sovereignty intensifies
CIO
DECEMBER 21, 2022
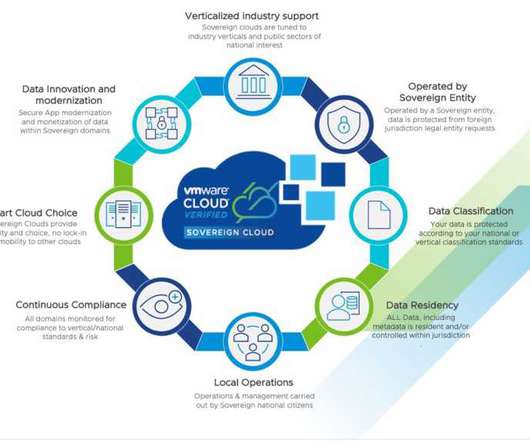
After Google’s cooperation with T-Systems and the “ Delos ” offer from Microsoft, SAP, and Arvato, AWS now follows suit. This is where VMware’s strategy is unique: VMware encourages multi-cloud and helps organizations maintain a cloud strategy that avoids lock-in and maintains quality and security while monitoring performance.

















































Let's personalize your content