Understanding Malware: A Guide for Software Developers and Security Professionals
The Crazy Programmer
OCTOBER 15, 2024
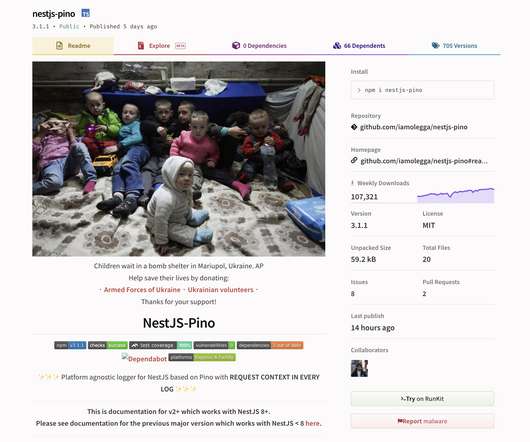
Malware or malicious software brings significant threats to both individuals and organisations. It is important to understand why malware is critical for software developers and security professionals, as it helps to protect systems, safeguard sensitive information, and maintain effective operations. What is Malware?















































Let's personalize your content