AI in the Enterprise: 5 key findings of AI usage and threat trends
CIO
MARCH 25, 2025
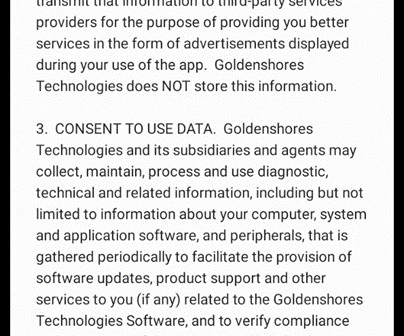
Additionally, ThreatLabz uncovered a malware campaign in which attackers created a fake AI platform to exploit interest in AI and trick victims into downloading malicious software. Traditional security approaches reliant on firewalls and VPNs are woefully insufficient against the speed and sophistication of AI-powered threats.







































Let's personalize your content