Koch CTO teams up to get cloud networking right
CIO
AUGUST 15, 2022
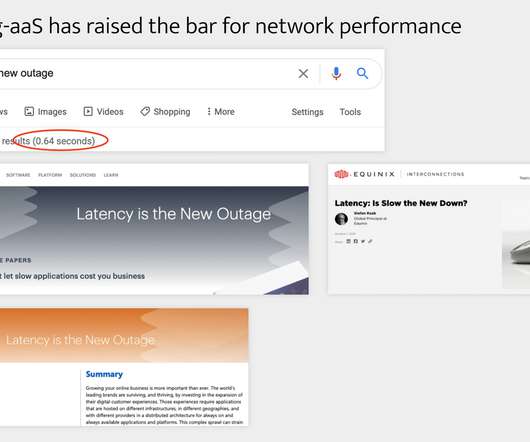
Cloud networking comprises three layers: first from on-premises data centers to the cloud, then within a cloud that has multiple accounts or virtual private clouds, and finally, between individual clouds in a multicloud environment. It’s more complicated than standard networking, Hoag says.
















Let's personalize your content