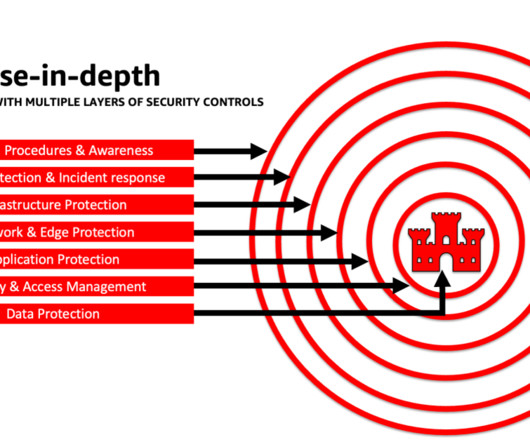
Governance and Fighting the Curse of Complexity
CIO
MARCH 20, 2024
The Burgeoning Complexity of IT and Security Solutions On a business level, complexity comes from growth through acquisition – when enterprises inherit systems of record and of work that, more often than not, are different from one another. There are also complex ERP and CRM solutions – as well as inputs from OT and IoT systems and devices.













































Let's personalize your content