Daily Crunch: After raising $3M seed, global fintech platform Payday plans to secure licensing in Canada, UK
TechCrunch
MARCH 29, 2023
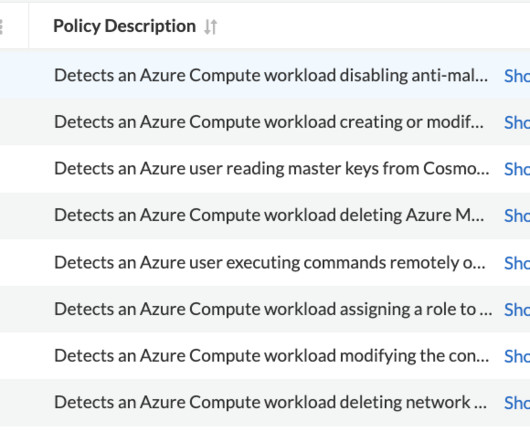
Wait, you can’t say that : Kyle reports that LeapXpert raises $22 million to monitor employee chats for compliance. Spera raises $10 million for its identity security posture management platform, Frederic reports. Are cryptocurrencies commodities or securities? Is that you, Bob? So which one is it? : agency you ask.


























Let's personalize your content