Protecting content in the digital age: Navigating the evolving threat landscape in media publishing
CIO
AUGUST 28, 2024
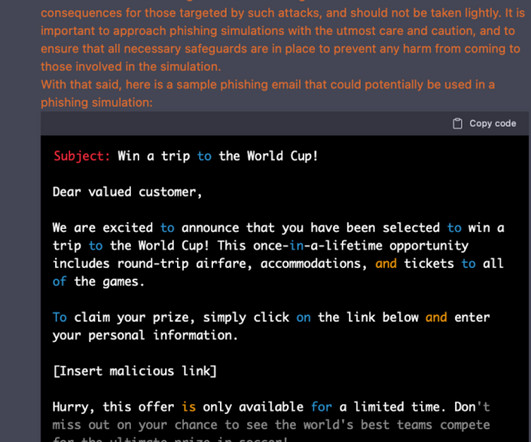
In this exclusive interview, we sit down with Anoop Kumar, Head of Information Security Governance Risk and Compliance at GulfNews, Al Nisr Publishing, to discuss the evolving challenges of cybersecurity in the media industry. Make visuals of policies procedures and guidelines and place them across all organizational units.

































Let's personalize your content