Tenable Bolsters Its Cloud Security Arsenal with Malware Detection
Tenable
MAY 1, 2024
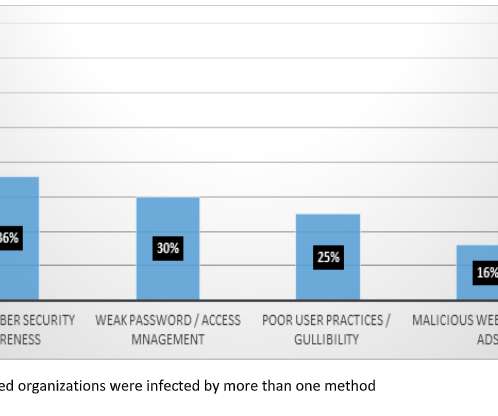
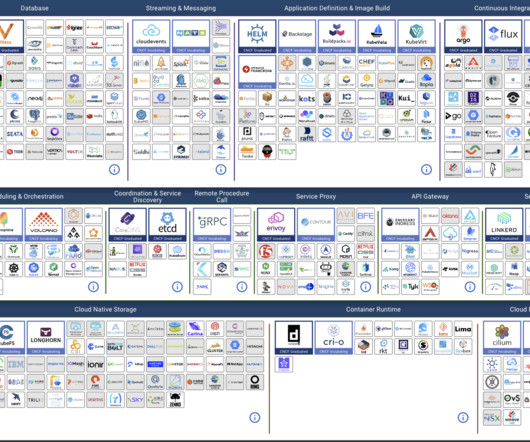
Tenable Cloud Security is enhancing its capabilities with malware detection. Combined with its cutting-edge, agentless vulnerability-scanning technology, including its ability to detect anomalous behavior, this new capability makes Tenable Cloud Security a much more complete and effective solution. Read on to find out how.









































Let's personalize your content