Digital addiction detox: Streamline tech to maximize impact, minimize risks
CIO
OCTOBER 17, 2024
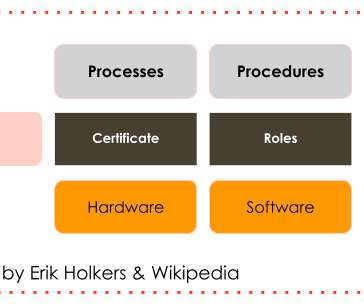
As Robert Blumofe, chief technology officer at Akamai Technologies, told The Wall Street Journal recently, “The goal is not to solve the business problem. These technologies often do not undergo a complete vetting process, are not inventoried, and stay under the radar. The goal is to adopt AI.”

















































Let's personalize your content