Patch Management Policy Features, Benefits and Best Practices
Kaseya
FEBRUARY 22, 2022
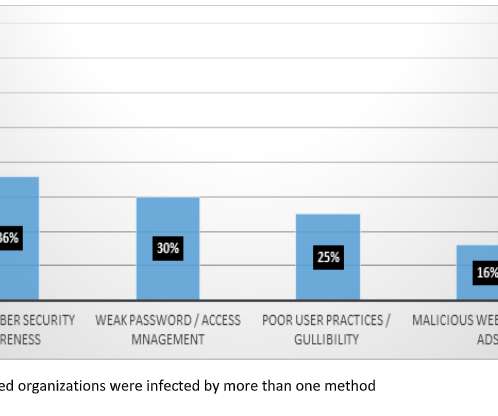
In this blog, we’ll discuss patch management policy best practices and explain how they contribute to a better patching environment for large and small organizations alike. What is a patch management policy? This is where patch management policies come into play. What is the importance of a patch management policy?













































Let's personalize your content