The Importance of Security and Compliance in Enterprise Applications
OTS Solutions
JUNE 21, 2023
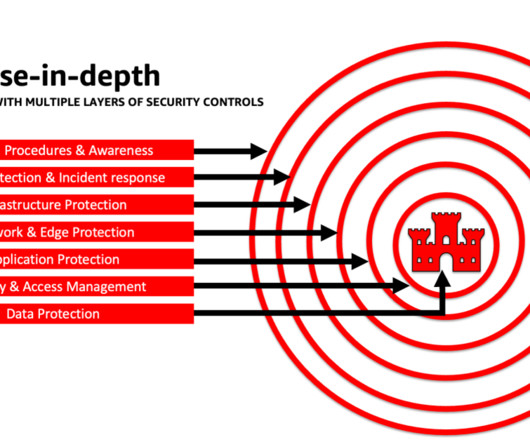
As DDoS attacks continue to evolve and become more sophisticated, organizations must take steps to protect their networks and ensure business continuity. This may include implementing advanced firewalls, deploying DDoS mitigation technologies, and establishing an incident response plan. A Comprehensive Guide.



















Let's personalize your content