3 Keys to ensuring your cloud provider offers a sound cyber security strategy
CIO
AUGUST 21, 2024
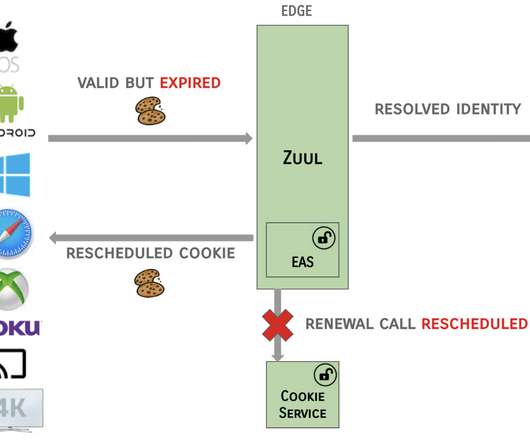
In practice, that could mean firewalls protecting the cloud perimeter, then identity management tools (authentication, authorization, accounting, or AAA) to ensure only authorized users are allowed in. Zero trust can also apply to other cloud infrastructure, including servers, databases, and applications.)















































Let's personalize your content