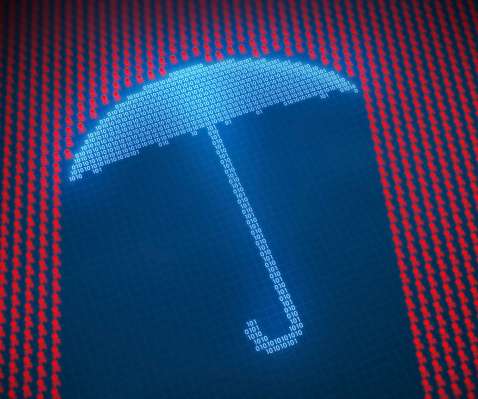
Case in point: taking stock of the CrowdStrike outages
CIO
APRIL 2, 2025
Last summer, a faulty CrowdStrike software update took down millions of computers, caused billions in damages, and underscored that companies are still not able to manage third-party risks, or respond quickly and efficiently to disruptions. It was an interesting case study of global cyber impact, says Charles Clancy, CTO at Mitre.











































Let's personalize your content