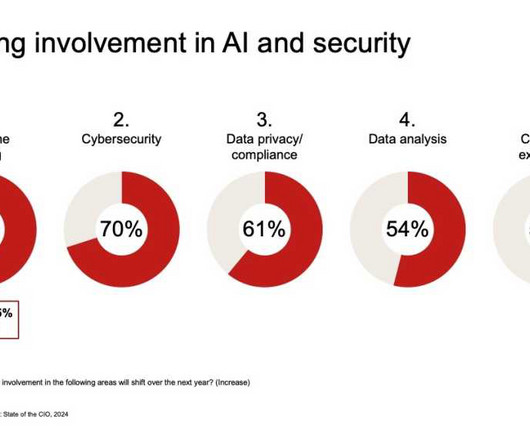
3 Keys to ensuring your cloud provider offers a sound cyber security strategy
CIO
AUGUST 21, 2024
Today, cloud providers may offer better cybersecurity protections than many companies can provide on-premises. The security professional shortage Some 3.5 million cybersecurity jobs are unfilled globally, with 750,000 of them in the U.S., according to researchers at Cybersecurity Ventures.



















































Let's personalize your content