How to manage cloud exploitation at the edge
CIO
JULY 17, 2023
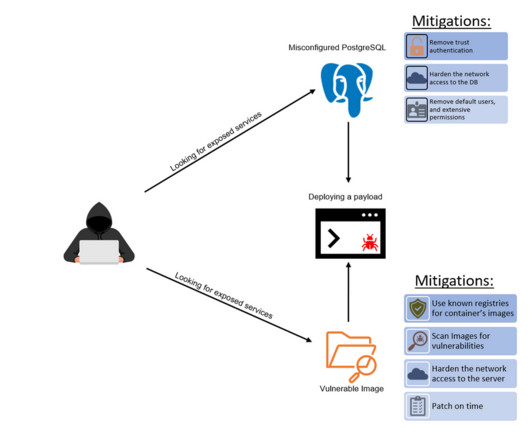
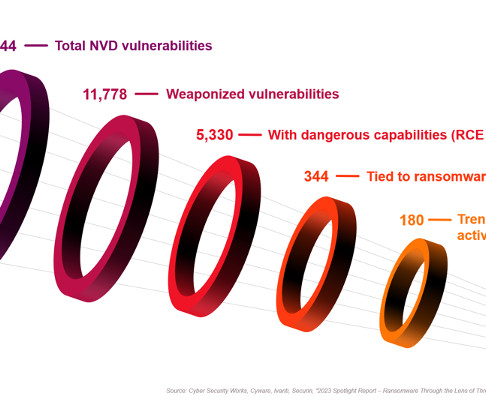
Common cloud exploitation outcomes Unauthorized Access: Attackers may attempt to gain unauthorized access to cloud accounts, systems, or data by exploiting weak or stolen credentials, misconfigurations, or vulnerabilities in the cloud environment. What can businesses do? Second, cyber criminals are well-organized and act fast.














































Let's personalize your content