Fixed wireless access (FWA) is a secure networking option
CIO
DECEMBER 19, 2023
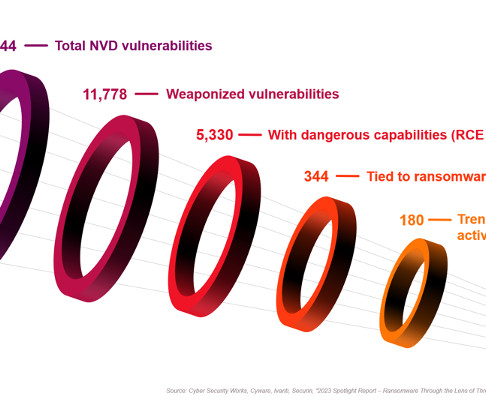
Hackers take advantage of out-of-date systems, software, and known security issues. However, outdated operating systems can be more vulnerable to security risks because they may lack the latest security updates and patches, serving as an entry point for hackers to infiltrate networks.













































Let's personalize your content