Make a resolution to clean up your digital act? Here’s how
The Parallax
DECEMBER 28, 2017
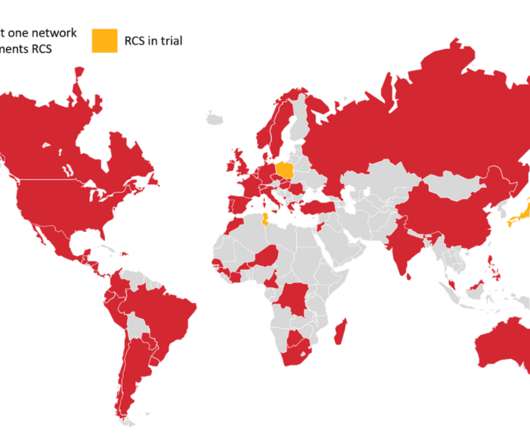
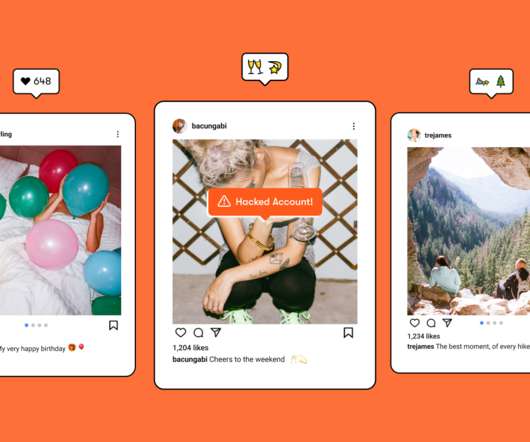
Step 1: Use two-factor authentication. In its most common form online, two-factor authentication makes you use a second, one-time password to access your account. If you can, segment your home Internet of Things devices on a separate network as well. Step 2: Use a VPN. Step 5: Keep your software up-to-date.








































Let's personalize your content