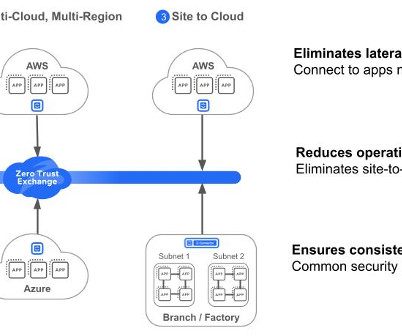
Why you must extend Zero Trust to public cloud workloads
CIO
NOVEMBER 8, 2023
It’s not as simple as just extending traditional firewall capabilities to the cloud. With Zscaler Workload Communications, organizations can effortlessly shift from traditional perimeter-based approaches to a zero-trust framework and establish granular control, strong authentication, and continuous monitoring. 8 Complexity.
















Let's personalize your content