How to Strengthen Active Directory and Prevent Ransomware Attacks
Tenable
AUGUST 3, 2021
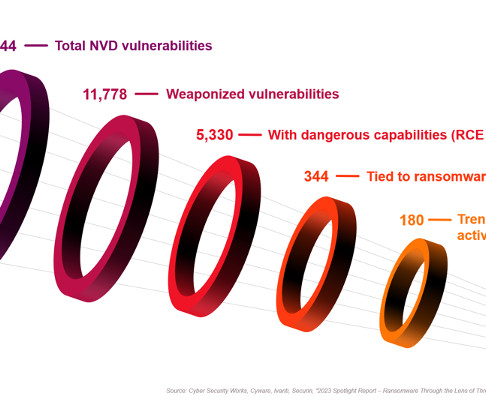
Ransomware attackers are initially compromising enterprises by one of two attack methods: Attackers are exploiting vulnerabilities within the hardware, operating systems, software, applications, etc. So, we'll say it again: patch your systems (and take your vitamins, too!). Trend 1: vulnerabilities and misconfigurations.

















Let's personalize your content