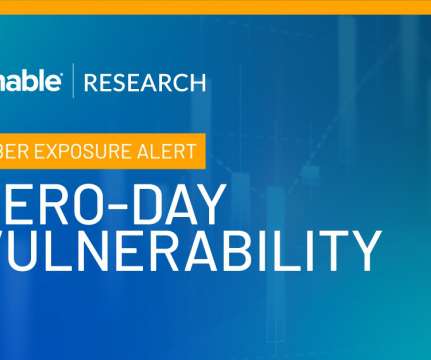
These Services Shall Not Pass: Abusing Service Tags to Bypass Azure Firewall Rules (Customer Action Required)
Tenable
JUNE 3, 2024
Azure customers whose firewall rules rely on Azure Service Tags, pay attention: You could be at risk due to a vulnerability detected by Tenable Research. Tenable Research has discovered a vulnerability in Azure that allows an attacker to bypass firewall rules based on Azure Service Tags by forging requests from trusted services.














































Let's personalize your content