Multi-Cloud Security Best Practices: How Companies Can Stay Protected
Tamnoon
MARCH 26, 2025
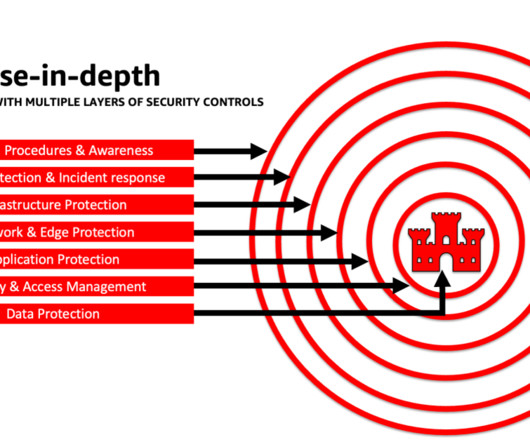
Instead, you need to authenticate and continuously validate the identity and validity of every user or device that accesses your ecosystem, working on the assumption that everyone is a potential threat actor, a principle known as zero trust access (ZTA). No Backups Resiliency and redundancy are two of the cloud’s greatest strengths.
















Let's personalize your content