More connected, less secure: Addressing IoT and OT threats to the enterprise
CIO
NOVEMBER 14, 2023
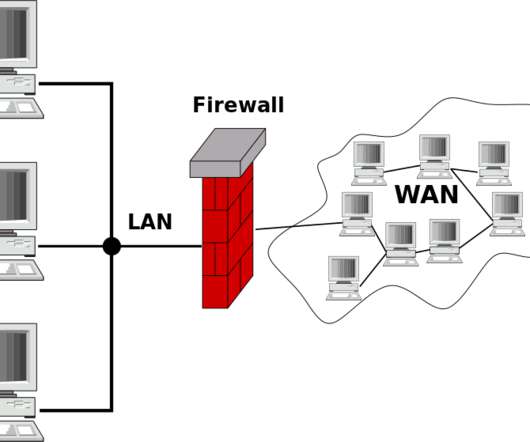
The Internet of Things (IoT) is a permanent fixture for consumers and enterprises as the world becomes more and more interconnected. By 2027, the global number of connected IoT devices is projected to exceed 29 billion, a significant increase from the 16.7 Your network becomes a breeding ground for threats to go undetected.

















































Let's personalize your content