5 key areas for tech leaders to watch in 2020
O'Reilly Media - Ideas
FEBRUARY 18, 2020
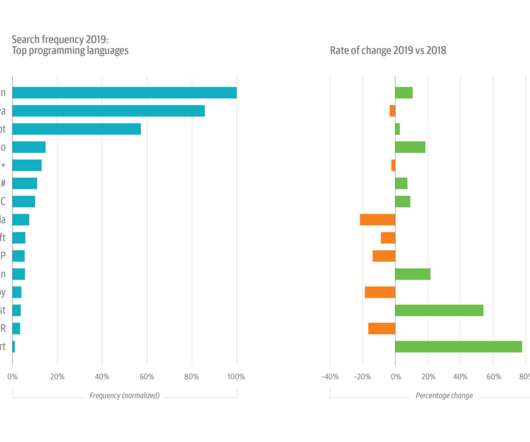
Growth is still strong for such a large topic, but usage slowed in 2018 (+13%) and cooled significantly in 2019, growing by just 7%. But sustained interest in cloud migrations—usage was up almost 10% in 2019, on top of 30% in 2018—gets at another important emerging trend. Security is surging. to be wary of.


















Let's personalize your content