Sesamm bags $37M to give corporates ESG insights using natural language processing
TechCrunch
MARCH 1, 2023
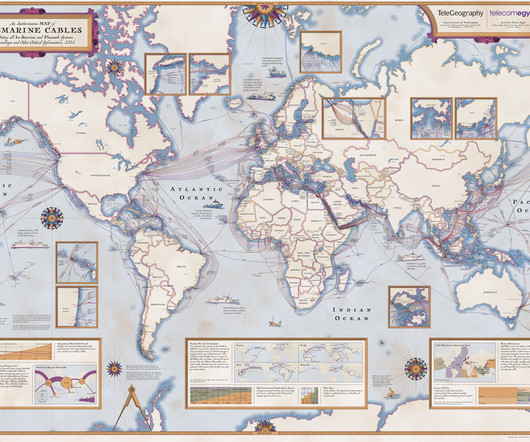
With that in mind, Sesamm enables businesses to track textual data from across the web — including news portals, NGO reports and social networks — and convert this into actionable insights. Elsewhere, private equity firms can use Sesamm for due diligence on potential acquisition or investment targets.













































Let's personalize your content